The following example modifies the ddos-protect application to use sFlow-RT's httpAsync() function to send events to Loki's HTTP API.
var lokiPort = getSystemProperty("ddos_protect.loki.port") || '3100'; var lokiPush = getSystemProperty("ddos_protect.loki.push") || '/loki/api/v1/push'; var lokiHost = getSystemProperty("ddos_protect.loki.host"); function sendEvent(action,attack,target,group,protocol) { if(lokiHost) { var url = 'http://'+lokiHost+':'+lokiPort+lokiPush; lokiEvent = { streams: [ { stream: { service_name: 'ddos-protect' }, values: [[ Date.now()+'000000', action+" "+attack+" "+target+" "+group+" "+protocol, { detected_level: action == 'release' ? 'INFO' : 'WARN', action: action, attack: attack, ip: target, group: group, protocol: protocol } ]] } ] }; httpAsync({ url: url, headers: {'Content-Type':'application/json'}, operation: 'POST', body: JSON.stringify(lokiEvent), success: (response) => { if (200 != response.status) { logWarning("DDoS Loki status " + response.status); } }, error: (error) => { logWarning("DDoS Loki error " + error); } }); } if(syslogHosts.length === 0) return; var msg = {app:'ddos-protect',action:action,attack:attack,ip:target,group:group,protocol:protocol}; syslogHosts.forEach(function(host) { try { syslog(host,syslogPort,syslogFacility,syslogSeverity,msg); } catch(e) { logWarning('DDoS cannot send syslog to ' + host); } }); }The highlighted code extends the existing scripts/ddos.js script to add Loki support. Add a panel to integrate the Loki log into the Grafana sFlow-RT DDoS Protect dashboard as shown at the top of this page.
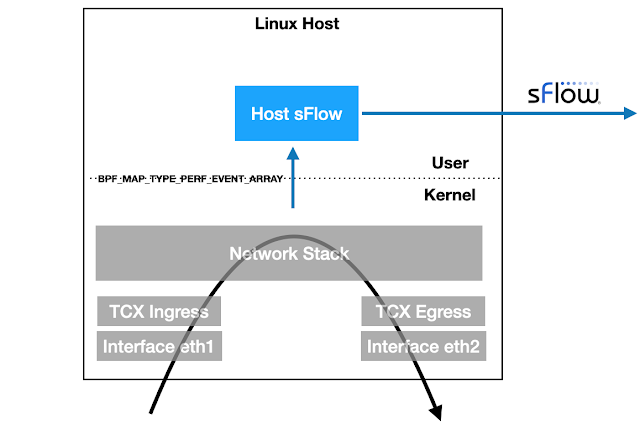
DDoS protection quickstart guide describes how to set up a DDoS mitigation solution using sFlow-RT.